The OSINT Newsletter - Issue #13
The OSINT Newsletter is back!
The return of The OSINT Newsletter may come as a surprise based on my last message. I’ve spent a couple of months reflecting on the projects that I enjoy and after making some adjustments, I’m now able to spend more time than I was able to previously working on things like The OSINT Newsletter, blogging, and perhaps podcasting in the future. If you want to hear the whole story, feel free to reach out to me on Twitter or LinkedIn.
Let’s get back to OSINT…
OSINT Tools
GitFive - Github
I’ve spent a lot of time lately in the vulnerability intelligence space. That has led me to think about a lot of applications for Github and OSINT. What I noticed is that there are a lot of malicious repositories being published on Github, some of them disguised as legitimate scripts but are in fact malware or similar. If you find yourself doing investigations into these types of issues, consider using GitFive.
GitFive is another great tool from the folks at Malfrats, specifically mxrch. They’re the people behind GHunt, Xueledoc, Holehe, and more. If you haven’t joined their Discord already, check it out at https://discord.gg/BZuE6SBe.
So, what does GitFive do?
My previous workflow was use Zen by S0md3v to reveal the email behind a Github repo, search that email address using the author-email: on Github, pivot to the commit history for network analysis, and reverse the email in tools like Epieos for identity resolution. GitFive takes it a step further.
Here are the main features:
Usernames / names history
Usernames / names variations
Email address to GitHub account
Find GitHub's accounts from a list of email addresses
Lists identities used by the target
Clones and analyze every target's repos
Highlights emails tied to GitHub's target account
Finds local identities (UPNs, ex : jeanpierre@My-Computer.local)
Finds potential secondary GitHub accounts
Doesn't need repos to work (but better)
Generates every possible email address combination and looks for matches
Dumps SSH public keys
JSON export
This is a massive amount of information! But what can you do with it?
Finding secondary accounts is pretty self-explanatory. More accounts, more attack surface. Enumerating possible email combinations and checking for other accounts is also handy. But the best part is that it stays within the API request limits of Github so you don’t get banned. From an offensive security perspective, you can also clone and analyze repos, finding vulnerabilities if that’s your thing.
Fig - fig.io
On the note of command line tools, if you find yourself not very comfortable with your command line, consider checking out Fig. When I first found Fig, it was only doing autocomplete for my terminal. Now it’s enhanced with AI and even lets you build your own custom commands, creating shortcuts for better efficiency.
If you’re not a power user of command line tools, no worries, Fig will help get you there (because you need to head that way). Following the autocomplete suggestions or learning from the AI’s automation will serve as training wheels to get you more comfortable with downloading scripts, exploring their capabilities, and maybe even building your own.
It’s free.
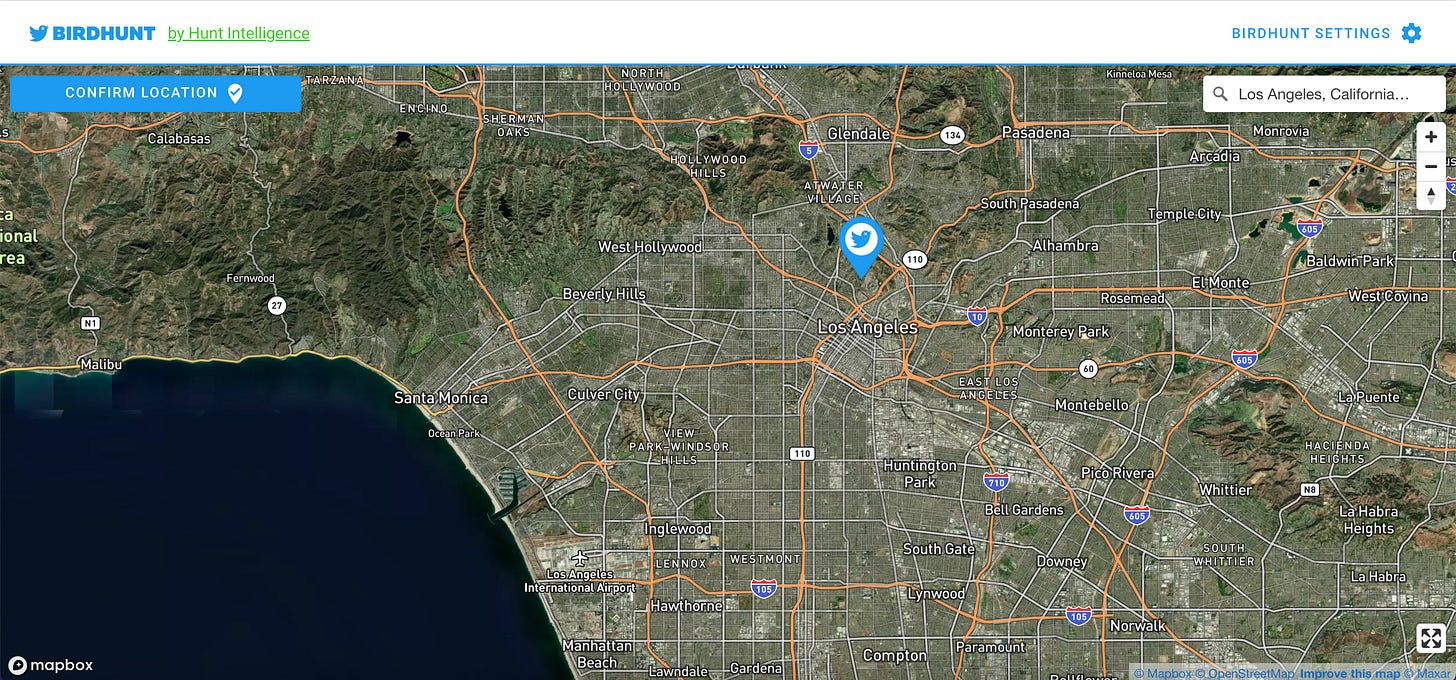
Birdhunt - birdhunt.co
In each newsletter I’ll try to share a script, a utility, and a web app for the folks out there that aren’t comfortable exclusively using the command line for OSINT research.
Birdhunt is one of many tools created by @LouisTomosEvans to help OSINT investigators find valuable information online. What does it do? It allows you to enter a location, specify the radius around that location you’d like to focus on, then it takes you to Twitter showing you posts from individuals in that area. This doesn’t come without risk. Because it focuses on the location of the user, not the location of the tweet itself, this is definitely a fuzzy match, as it relies on the idea that both the Twitter user’s location is accurate and that they are ‘home’ at the time of the tweet.
Of course, you could just use the operator geocode:<latitude>,<longitude>,<radius (km)> and get the same result just using Twitter, but this is still a good tool to bookmark to automate that process without the need to memorize that format.
Geolocation is almost dead, but sometimes you’re hunting for snipe.
Remember #OSINT != tools. Tools help you plan and collect data but the end result of that tool is not OSINT. You have to analyze, verify, receive feedback, refine, and produce a final, actionable product of value before it can be called intelligence.
This is the end of the free subscription to The OSINT Newsletter. To see practical applications of OSINT tactics and techniques, please consider supporting this publication with a paid subscription.
Paid subscribers get access to practical OSINT tactics and techniques I haven’t published publicly online. This issue explores practical applications of the tools previously mentioned in addition to step-by-step guides for OSINT techniques.